Get in touch
2543934363
gsatactical@gmail.com
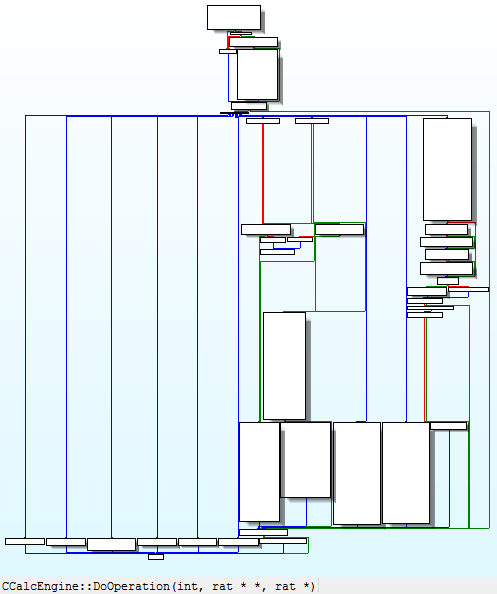
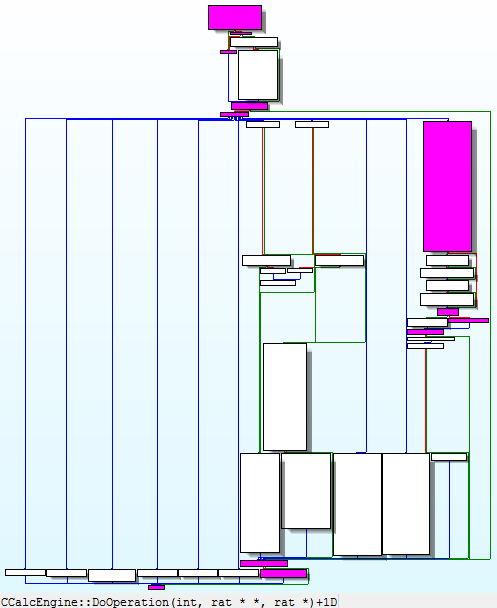
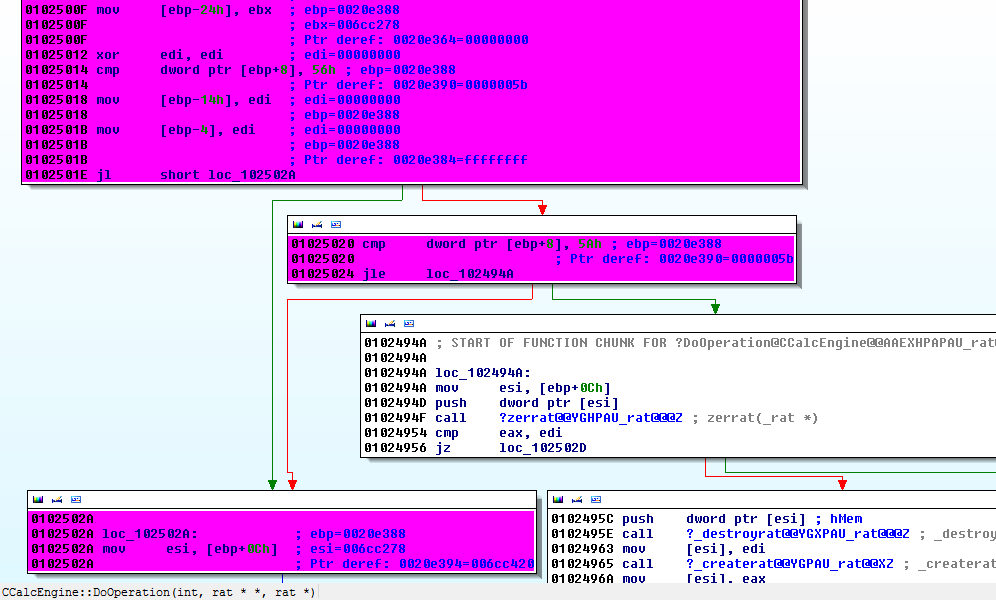
Integrating WinDbg and IDA for Improved Code Flow Analysis
Matt • July 30, 2011
00495001 calc!CCalcEngine::DoOperation =
0:000> BP 00495001
0:000> g
Entering in 1000 / 4 in calc
Step through function until return instruction
The following dump is the result of the operation 1000/4 in the function without stepping into calls (using the PA command):
Hopefully, by now you can see the power of IDApython in improving your analysis workflow. If you use this script, I welcome your feedback!
References:
1. Cody Pierce, “MindshaRE: Hit Tracing in WinDbg,” July 17, 2008, http://dvlabs.tippingpoint.com/blog/2008/07/17/mindshare-hit-tracing-in-windbg

By ron
•
June 27, 2023
Recently, I had the privilege to write a detailed analysis of CVE-2023-34362, which is series of several vulnerabilities in the MOVEit file transfer application that lead to remote code execution. One of the several vulnerabilities involved an ISAPI module - specifically, the MoveITISAPI.dll ISAPI extension. One of the many vulnerabilities that comprised the MOVEit RCE was a header-injection issue, where the ISAPI application parsed headers differently than the .net application. This point is going to dig into how to analyze and reverse engineer an ISAPI-based service! This wasn’t the first time in the recent past I’d had to work on something written as an ISAPI module, and each time I feel like I have to start over and remember how it’s supposed to work. This time, I thought I’d combine my hastily-scrawled notes with some Googling, and try to write something that I (and others) can use in the future. As such, this will be a quick intro to ISAPI applications from the angle that matters to me - how to reverse engineer and debug them! I want to preface this with: I’m not a Windows developer, and I’ve never run an IIS server on purpose. That means that I am approaching this with brute-force ignorance! I don’t have a lot of background context nor do I know the correct terminology for a lot of this stuff. Instead, I’m going to treat these are typical DLLs from typical applications, and approach them as such.
By Richard Bejtlich
•
June 25, 2023
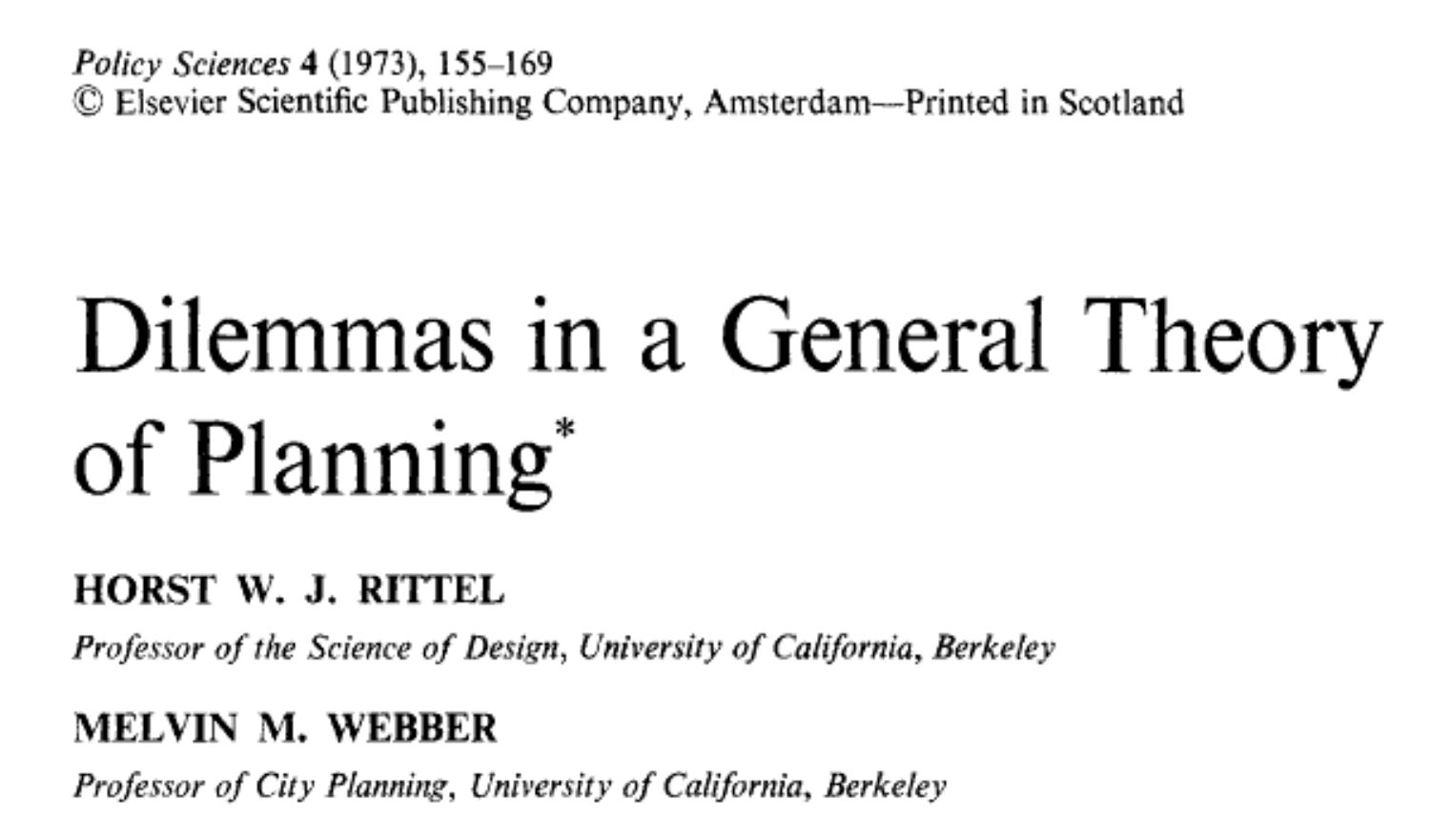
Cybersecurity is a social and policy problem, not a scientific or technical problem. Cybersecurity is also a wicked problem. In a landmark 1973 article, Dilemmas in a General Theory of Planning , urban planners Horst W. J. Rittel and Melvin M. Webber described wicked problems in these terms:
#GSASECURITY
3416, 13th Street Suite #201, Washington, DC, 20032
www.gsasecurity.org
(254) 393-4563
© 2025
All Rights Reserved | Dude Designz DC